Debugging File upload / multipart upload and other HTTP requests
Sometimes you want to see the request as it is received by the server, without any handling / obscuring of the original request.
For instance, to see whether different browsers handle file uploads differently.
On the other hand, you do not want to write up your own mockup server, just to handle these requests, or install complicated software.
Unfortunately netcat will not do without additional wrapping in a bash script. Therefore I went looking for something else!
Docker http request echo container
There is a Docker container, which allows you to echo your request data as JSON. It is very useful for debugging:
https://github.com/mendhak/docker-http-https-echo
It also accepts POST messages.
Installation
docker run -p 8080:80 -p 8443:443 –rm -t mendhak/http-https-echo
Example
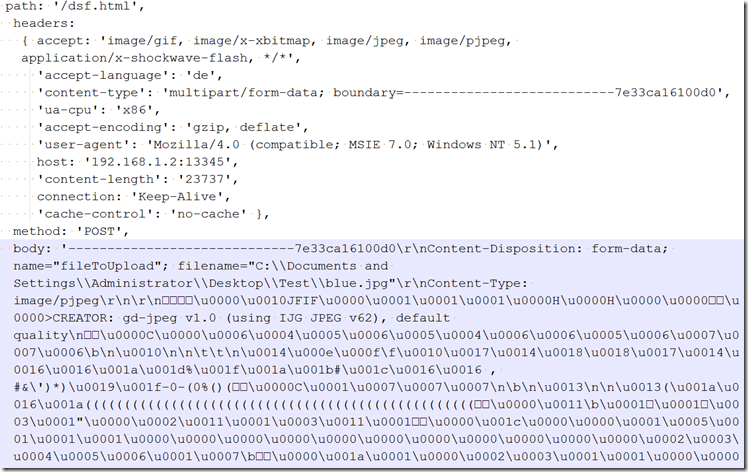
Here’s a reply to a sample upload request.
Note the Content-Disposition, and the boundaries in the request body.
The request was done using Internet Explorer 7 on a Windows XP (virtual machine).
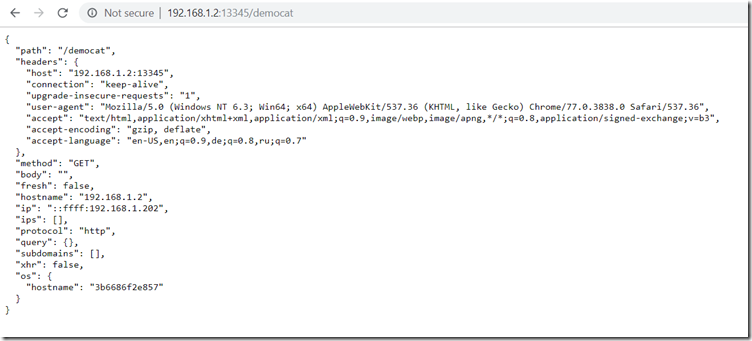
and another screenshot showing a plain vanilla get request (from Windows 8.1):
—————————–7e33ca16100d0\r\nContent-Disposition: form-data; name=”fileToUpload”; filename=”C:\\Documents and Settings\\Administrator\\Desktop\\Test\\blue.jpg”\r\nContent-Type: image/pjpeg\r\n\r\n����\u0000\u0010JFIF\u0000\u0001\u0001\u0001\u0000H\u0000H\u0000\u0000��\u0000>CREATOR: gd-jpeg v1.0 (using IJG JPEG v62), default
(…)
\u0000���\r\n—————————–7e33ca16100d0\r\nContent-Disposition: form-data; name=”submit”\r\n\r\nUpload Image\r\n—————————–7e33ca16100d0–\r\n’,
How to get Windows XP & IE 7
Microsoft used to have a virtual machine for testing website compatibility with IE 7. This is gone now, unfortunately.
There is, however, a possibility to get Windows XP straight from Microsoft (extracting a virtual image from the XP mode for Windows 7):
https://parsiya.net/blog/2017-12-19-windows-xp-32-bit-sp3-virtual-machines/
It will work for 30 days.
And you can get the download for Internet Explorer 7 here:
http://download.microsoft.com/download/3/8/8/38889dc1-848c-4bf2-8335-86c573ad86d9/IE7-WindowsXP-x86-enu.exe
(extracted from this script: https://raw.githubusercontent.com/xdissent/ievms/master/ievms.sh )